Hacker computer screen. Source: TechGaged / Shutterstock
Crypto Apps Exposed to Risk After Malicious Axios Versions Go Live
In Brief
- • Malicious Axios versions exposed apps to a supply chain attack.
- • Crypto projects may be affected due to widespread usage.
- • The incident highlights growing risks in open-source dependencies.
A supply chain attack has hit Axios, one of the most widely used JavaScript packages on npm, after malicious versions went live with a hidden dependency. Socket says the poisoned releases pulled in a package it identified as malware, and warned that projects using caret ranges could have installed it automatically. Axios has roughly 100 million weekly downloads, which turns one bad publish into a potentially huge blast radius, especially for crypto apps that rely on it for API communication.
What happened in the Axios compromise
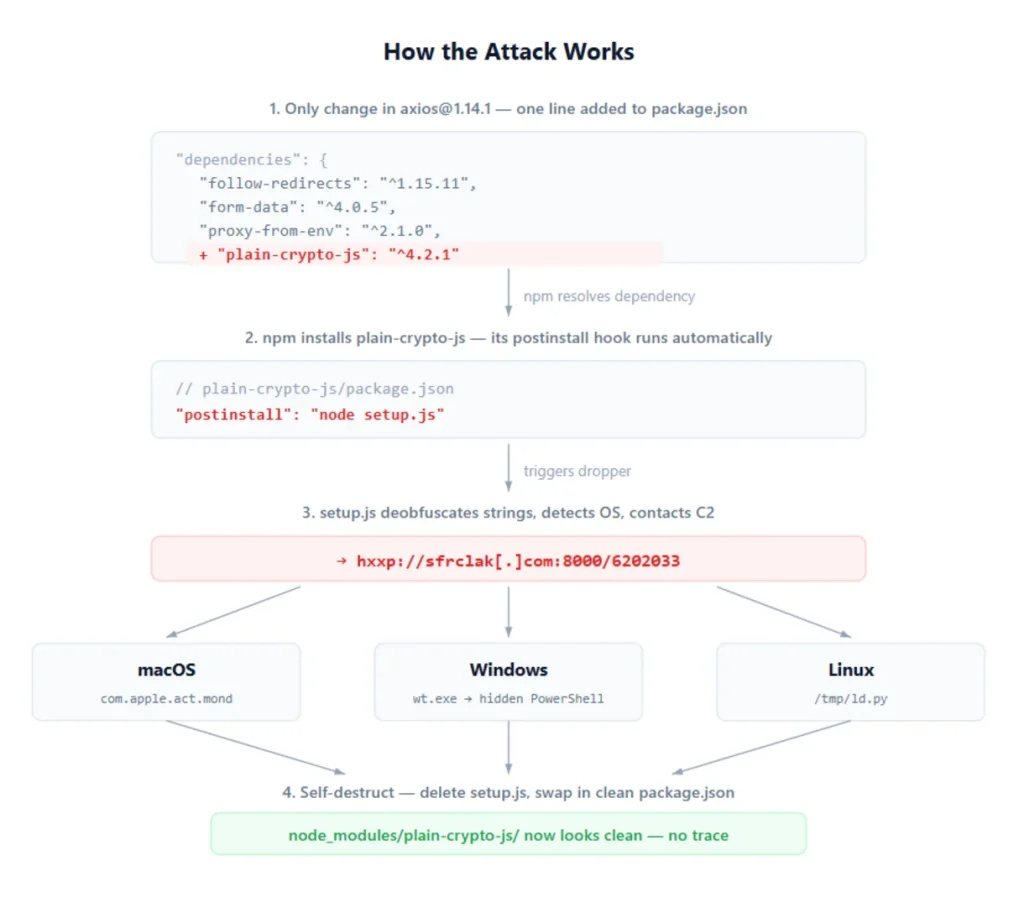
According to the researchers from Socket Security, including the CEO and co-founder Feross Aboukadijeh, the malicious dependency was published minutes before the compromised Axios versions and was then injected into both the 1.x and 0.x branches within 39 minutes of each other.
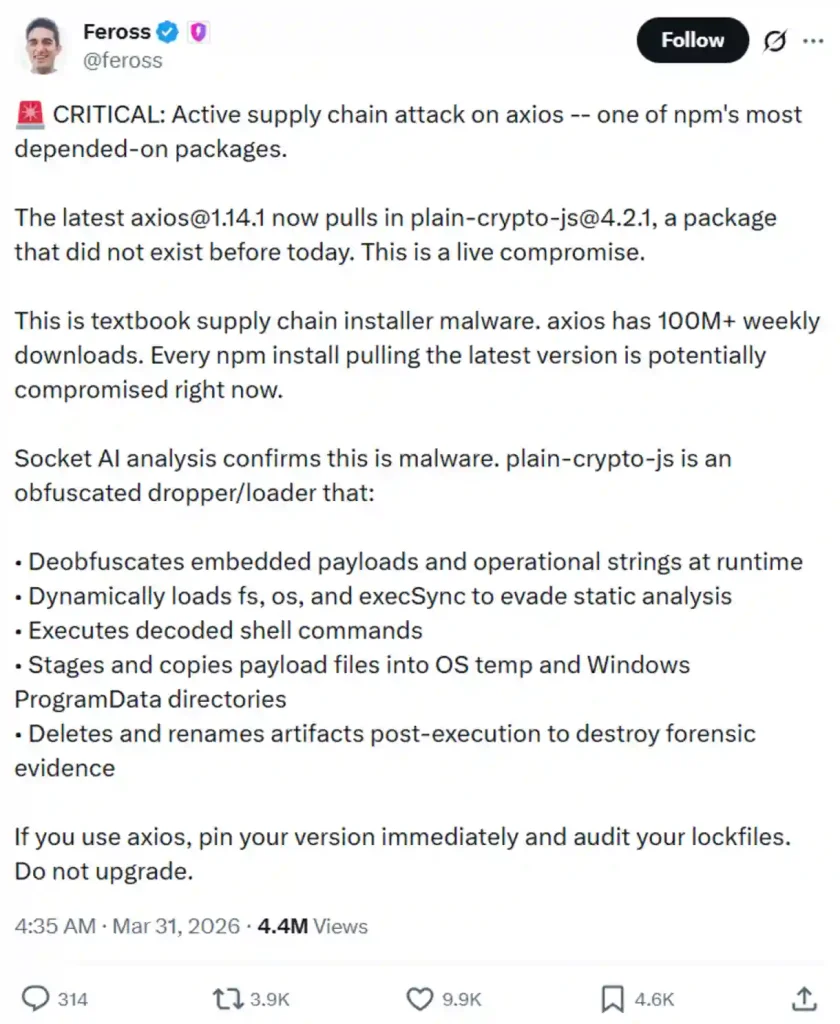
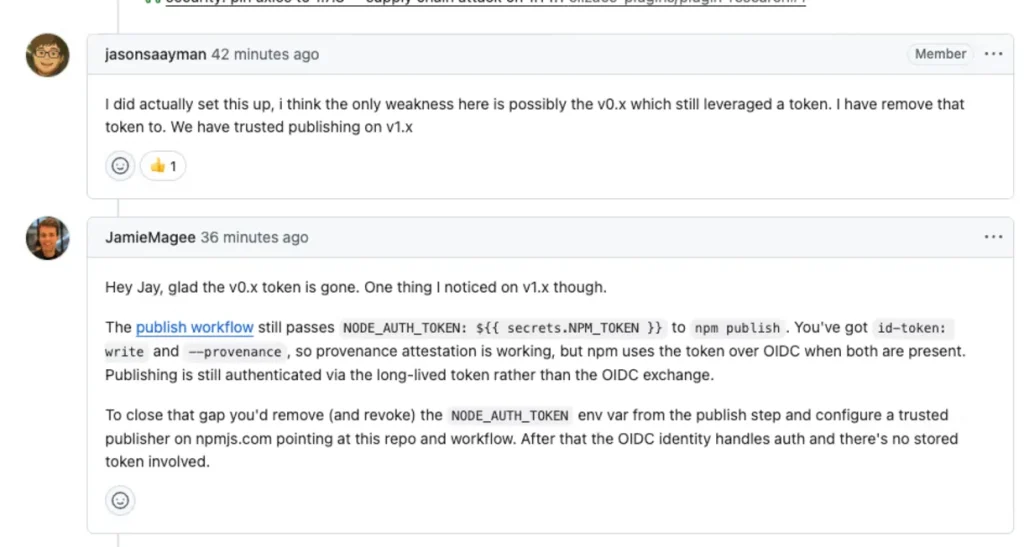
As they explained on March 31, the affected versions did not appear in Axios’ normal GitHub release flow, which raised immediate suspicion that the publish happened outside the project’s standard process. A GitHub issue in the Axios repo also warned that axios@1.14.1 and axios@0.30.4 were compromised and suggested maintainer accounts may have been taken over.
Socket says the dropper ran through a postinstall hook, decoded obfuscated payloads at runtime, and fetched platform-specific malware. Its analysis says the campaign targeted macOS, Windows, and Linux, with the macOS path delivering a full remote access trojan capable of running commands and deploying additional binaries.

Why this attack is a bigger warning for developers
The immediate advice is simple: check lockfiles for axios@1.14.1, axios@0.30.4, and plain-crypto-js@4.2.1, then roll back if they appear. Socket also warned that the malware cleaned up after itself by deleting and renaming files, which means developers may not find obvious traces just by inspecting node_modules after the fact.
However, the even bigger problem is speed. One popular package, one compromised publish path, and one transitive dependency were enough to put a huge chunk of the JavaScript ecosystem, including a massive number of crypto apps, at risk.
That is exactly the kind of weakness attackers want, and it is getting more dangerous as AI-assisted coding increases the amount of code written and the number of dependencies pulled in without close review, according to Aboukhadijeh’s public comments summarized in this developing incident.
How do you rate this article?
Subscribe to our YouTube channel for crypto market insights and educational videos.
Join our Socials
Briefly, clearly and without noise – get the most important crypto news and market insights first.
Also read
Similar stories you might like.