Masked hacker laptop. Source: TechGaged / Shutterstock
Solana-Based Drift Protocol Halts Operations After Security Breach; What Happened?
In Brief
- • Drift Protocol halted operations after a $280M exploit.
- • Attackers targeted governance approvals, not smart contracts.
- • The breach highlights risks in multisig and signing processes.
Drift Protocol halted deposits and withdrawals after attackers drained roughly $280 million through an admin-level exploit. The Solana-based DEX confirmed the breach involved a takeover of its Security Council permissions using pre-approved transactions. The incident highlights how, beyond smart contracts, governance and signing processes have become a primary attack surface in DeFi.
Attack bypassed smart contracts, targeted governance
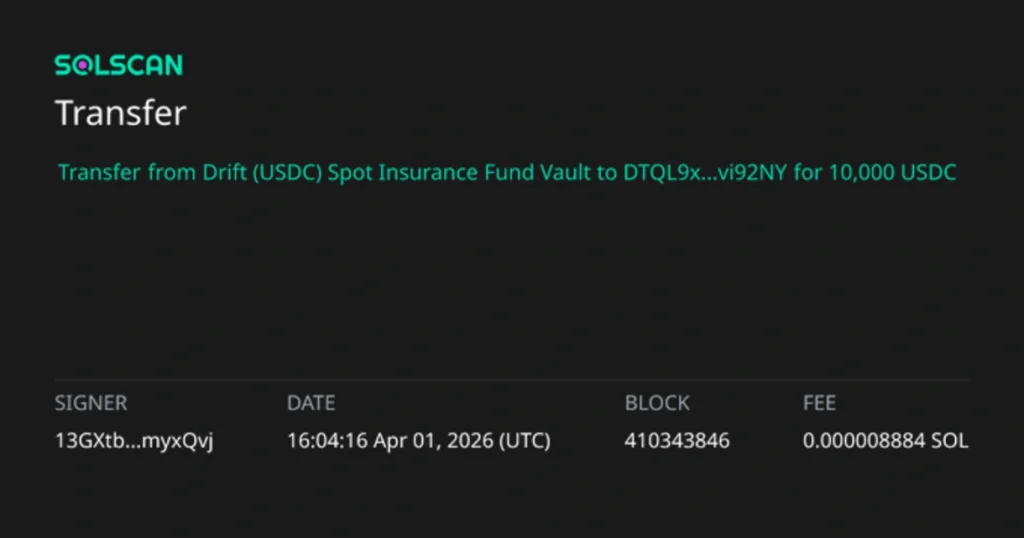
According to reports by Drift Protocol, shared in a series of X posts on April 2, the attacker gained control by abusing multisig approvals tied to durable nonce accounts, a Solana feature that allows transactions to be pre-signed and executed later.

According to the team, at least two out of five required multisig signers had unknowingly approved transactions ahead of time. Those approvals were then used to execute a malicious admin transfer within minutes.
Once in control, the attacker introduced a malicious asset and removed withdrawal limits, allowing funds to be drained quickly.
Drift described the operation as highly coordinated, involving weeks of preparation and staged execution. The use of pre-signed transactions meant the final attack looked legitimate at the moment of the execution.

What the breach affected and what happens next
The breach impacted funds in lending, vaults, and trading accounts on the platform. Drift said some assets remain unaffected, including tokens not deposited into the protocol and funds in the insurance pool, which are now being moved out as a precaution.

The platform has frozen all core protocol functions and removed the compromised multisig wallet. The team is now working with security firms, exchanges, and law enforcement to trace and potentially freeze stolen assets.
But, the bigger issue is structural. This attack shows that even when smart contracts hold up, human-layer approvals and governance workflows can still fail. Pre-signed transactions, social engineering, and delayed execution mechanisms are becoming more common tools for attackers.
All things considered, this whole incident goes to show that security in DeFi is now about who signs what, and when, and no longer ‘just’ about the code, something active participants in the crypto sector should take onboard going further.
How do you rate this article?
Subscribe to our YouTube channel for crypto market insights and educational videos.
Join our Socials
Briefly, clearly and without noise – get the most important crypto news and market insights first.
Also read
Similar stories you might like.